An Access Control List (ACL) contains metadata that specifies who is allowed to view and modify a document. Each item in a repository has an associated ACL that is updated whenever a user changes the permissions applied to the item.
Connectors that support mapped security extract ACLs from the repository. The connector adds an encrypted ACL to a document metadata field, usually AUTONOMYMETADATA, for every document that is ingested. IDOL Server uses ACLs to provide document security.
There are different ACL formats, used with different security types. This section describes a typical “NT-style” ACL.
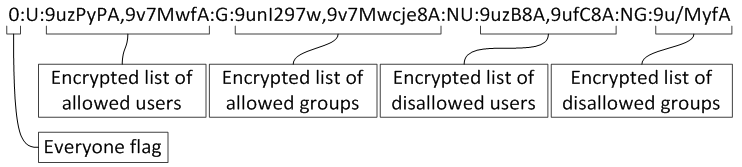
A typical ACL might look like this:
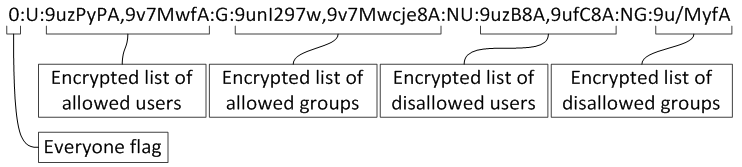
The ACL begins with a 0 or a 1 (the Everyone flag) and is followed by four sections:
| U | Allowed users |
| G | Allowed groups |
| NU | Disallowed (or "negative") users |
| NG | Disallowed (or "negative") groups |
These sections each hold comma separated lists of encrypted strings. Each string holds a user name or the name of a group, for example:
DOMAIN\person1,DOMAIN\person2
is encrypted and becomes:
9uz4+eLj4uD08d3I397Cw5zw,9uz4+eLj4uD08d3I397Cw5/w
Only the values in the comma-separated list are encrypted, and not the commas.
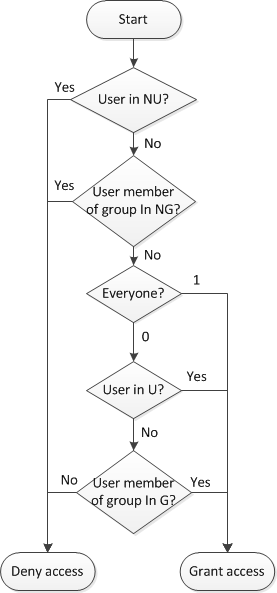
When the ACL is interpreted, the disallowed users and groups are always given priority. A user is not allowed to view a document if they are in the list of disallowed users (NU) or if they belong to a group in the list of disallowed groups (NG).
If the user has not been explicitly denied access, the rest of the ACL determines whether they are granted access to a document. If the Everyone flag is 0 they are granted access only if their user name appears in the list of allowed users (U), or if they are in a group that appears in the list of allowed groups (G). If the Everyone flag is 1 the user is granted access, regardless of whether they appear in those lists (U or G).
This process is summarized in the following diagram:
For troubleshooting, you can set EncryptACLEntries to False in the connector to leave the ACLs unencrypted. This allows you check that the metadata that the connector produces has the expected ACL. However, you cannot use this unencrypted security information in the Content component index. Decrypt ACLs for troubleshooting purposes only.
|
|