An online cyberthreat experience
Accelerate threat detection and response with holistic security analytics, native SOAR, and intelligent automation.
Do more in less time with intelligent end-to-end automation.
Focus on threats that matter with 360° security analytics.
Predictable costs. Cloud or on-premises deployment.
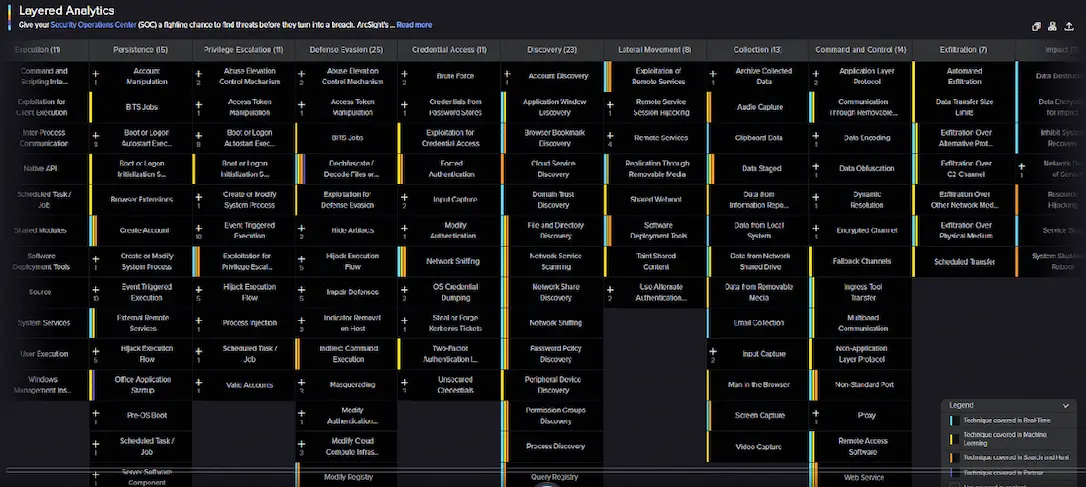
Real-time correlation + hypothesis- and analytics-based threat hunting = contextually rich insights.
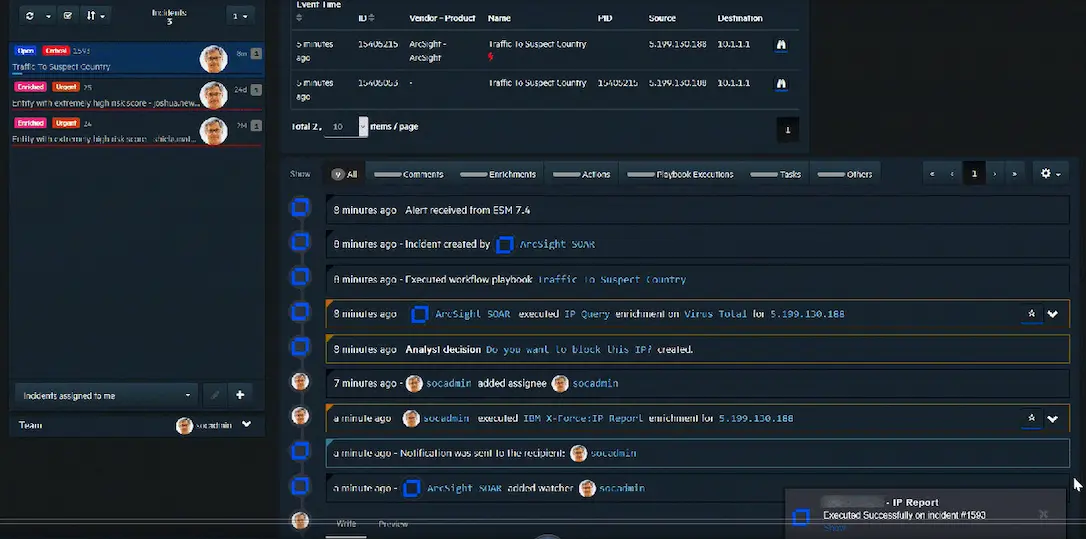
Fully integrated native Security Orchestration Automation and Response to accelerate response and streamline investigation.
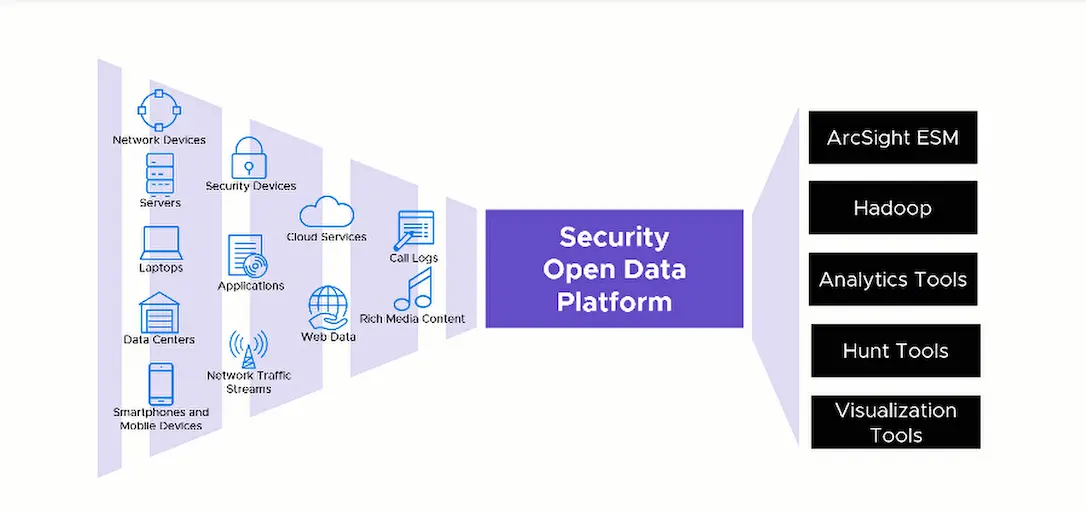
Extensive data connectivity and robust data enrichment for diverse, rapidly expanding data sources.
Optimize your SOC with a unified automation and analytics platform that intelligently adapts to the threat landscape.
Reduce total exposure time and empower analysts to focus on threats that matter by accelerating detection and response.
Defend against social engineering and rogue employees with contextual intel on high-risk users and vulnerable entities.
Address known and unknown threats with relevant threat insights and minimal false alerts using comprehensive security analytics.
Simplify log management and reporting with unified storage, fast queries, and customizable reports and dashboards.
One stop to harness the powers of real-time correlation, hypothesis-based threat hunting, and behavioral analytics.
Discover, define, and contextualize adversarial internet signals directed at your organization with cyDNA.
Out-of-the-box Security Orchestration Automation and Response enables automated, orchestrated, and accelerated incident response.
Unified storage, fast big-data search, rich analytics, visualization, and reporting accelerate threat hunting and ease compliance.
Extensive coverage of MITRE ATT&CK techniques and tactics with layered analytics and threat monitoring content packages.
Real-time data collection and enrichment. Simplified management of devices, connectors, and destinations.
Real-time threat detection, analysis, and response in a powerful, adaptable, and comprehensive SIEM solution.
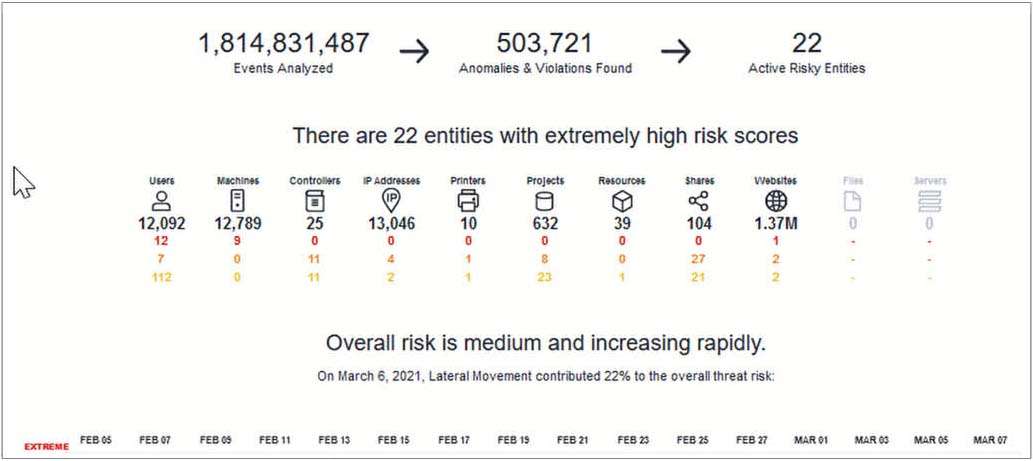
Advanced threat detection using behavioral analytics to detect insider threats and advanced persistent threats (APTs).
Comprehensive SIEM log management and security analytics solution to ease compliance burdens and accelerate forensic investigation.
Empowers your security operations with automated and orchestrated incident response. Provides a central hub for existing security tools.
Awareness beyond your perimeter, specific and actionable intelligence for complex operating environments.
Real-time threat detection, analysis, and response in a powerful, adaptable, and comprehensive SIEM solution.
Advanced threat detection using behavioral analytics to detect insider threats and advanced persistent threats (APTs).
Comprehensive SIEM log management and security analytics solution to ease compliance burdens and accelerate forensic investigation.
Empowers your security operations with automated and orchestrated incident response. Provides a central hub for existing security tools.
Awareness beyond your perimeter, specific and actionable intelligence for complex operating environments.
Fernando Mitre
Partner, Cybersecurity & Privacy
Large Online Retailer
Chief Information Security Officer