Viewing open source data
After you download, install, and enable the OpenText Core SCA or Sonatype parser plugin for Application Security, you can view the open source vulnerability data uploaded for an application version. You can view the results uploaded for an application version either from the AUDIT page, or from the OPEN SOURCE page.
Viewing open source data from the AUDIT page
To view open source vulnerability results from the AUDIT page:
- On the header, select Applications.
Select the application version for which open source results have been uploaded.
From the Group by list on the AUDIT page, select Analysis Type.
Expand the DEBRICKED or SONATYPE header, and then expand the row for a result you want to examine.
For detailed information about how to interpret OpenText Core SCA vulnerability data displayed, see the Debricked documentation. For information about how to interpret Sonatype vulnerability data displayed, see the Sonatype documentation.
For information about how to audit open source results, see Auditing analysis results.
Viewing open source data from the OPEN SOURCE page
To view open source results from the OPEN SOURCE page:
- On the header, select Applications.
Select the application version for which open source results have been uploaded.
Click OPEN SOURCE.
The OPEN SOURCEpage is visible only if open source results have been uploaded for the selected application version. In the OPEN SOURCE COMPONENTS table, click the row for an issue you want to examine.
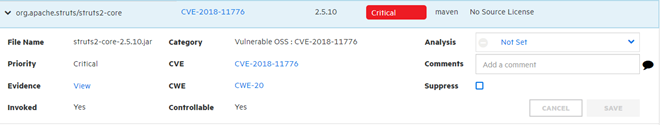
The following table contains descriptions of the details shown.
Field Description File Name Name of the component file in which the issue was discovered. Category OSS index category: Common Vulnerabilities and Exposures ID Analysis (or other assigned primary tag) If you audit the issue from the OPEN SOURCE page, you can select a primary tag value to assign from this list. Priority Fortify priority rating CVE CVE (Common Vulnerabilities and Exposures) ID number assigned to the vulnerability. Click the link to go directly to a highly detailed description of that vulnerability on the CVE site. Comments If you audit the issue from the OPEN SOURCE page, you can add comments. Evidence A link to any evidence if the vulnerability is invoked or controllable. CWE Common Weakness Enumeration. Click this link (if present) to go to the Common Weakness Enumeration website and see details about the software weakness type uncovered. Suppress Select this check box if you think that the issue is not of concern. For more information about issue suppression, see About suppressed, removed, and hidden issues.
Invoked This field shows whether the issue was invoked in the code. Controllable This field shows whether or not user-controlled input reaches the method or function.
For detailed information about how to interpret the OpenText Core SCA vulnerability data displayed, see the Debricked documentation. For information about how to interpret Sonatype vulnerability data displayed, see the Sonatype documentation.
See Also