22.1 Understanding the process flow
Figure 22-1 Review process
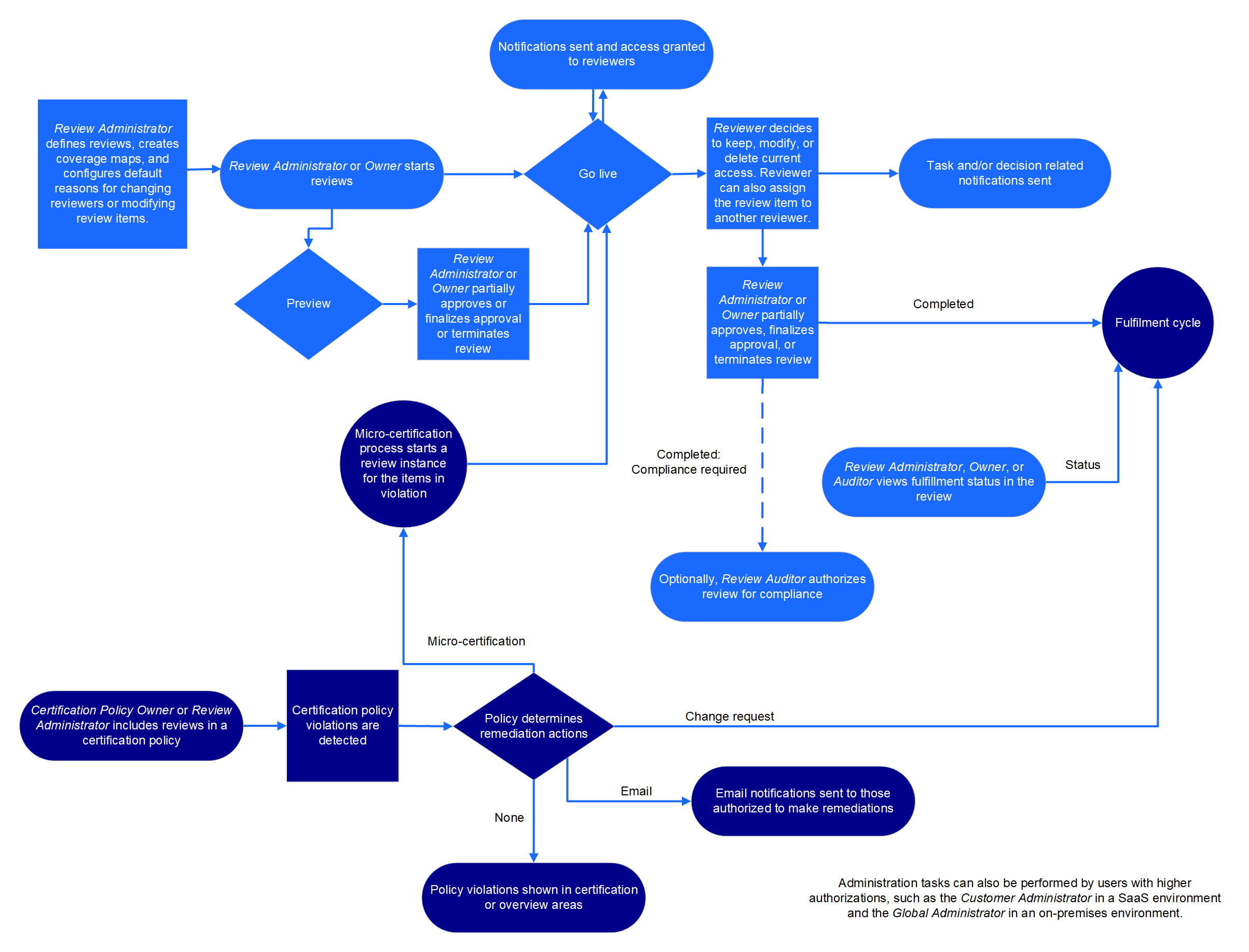
Reviews provide a way to monitor access to your business systems. Many users take part in the overall review process:
-
Review Administrators create review definitions, preview review definitions, and manage reviews.
-
(Optional) Review Administrators can request Data Administrators to configure additional selection criteria such as custom identity, permissions, permission assignment, or business role attributes for selecting review items and refine review definitions.
-
Review owners start, preview, monitor, complete, and terminate reviews.
-
Reviewers, such as supervisors and application owners, act on review items.
-
Escalation reviewers review items in the exception queue
-
Fulfillers manage change requests.
-
Auditors accept or reject completed reviews.
-
Review or Data Administrators create certification policies to check for violations and set remediation action which triggers remediations including micro certifications (focused reviews)
For more information about authorizations, see Section 2.0, Adding OpenText Identity Governance users and assigning authorizations.
NOTE:The OpenText Identity Governance server needs a 30-minute gap between runs of the same review. For example, you terminate a scheduled review that is in progress. To schedule that review to run again, allow at least 30 minutes to lapse after terminating the previous run. Otherwise, the second run fails to start and the application does not notify you of the failure.
22.1.1 Viewing the catalog
Before creating or editing review definitions, reviewing the data in the catalog will help determine who needs to be included in the reviews and which items should be reviewed. Some examples of the information a Review Administrator, Customer Administrator, or Global Administrator can look for are:
-
Attributes of the user that may not be available in the Quick Info (view of an item, such as a user or a role, when you click on it) to help determine whether the person should be included in a review or not
-
The last review date of an account
NOTE:This date reflects the date when an account was last reviewed as part of an Account Review. Review of a user’s access to an account as part of a User Access Review does not impact this date.
-
Risk levels of users or permissions
-
Association with an application
-
Group, business role, or technical role membership
-
Certification status of a user, specifically the date the user was last certified, and details of last review decisions and certification policy violations
22.1.2 Understanding review definitions
You can run a review once or multiple times either by starting the review manually or by scheduling it to start at the specified time or interval. Each review is based on a review definition that is based on a specific type of review object and defines all parameters for that particular review. Review Administrators, Customer Administrators, or Global Administrators create review definitions using the provided default review definitions with preselected criteria. These definitions enable you to select what you want to review. For example, you can select review objects such as User profiles, Technical role assigned to users, Accounts and their permissions, or Business roles assigned to users. These review objects are specific to a review type (review template). Each review type provides selection criteria that help Review Administrators to focus their reviews based on varying combinations of identity, application, account, permission, permission assignment, or business role attributes. For example, you can focus the User profiles review by specifying that reviewers should review users with risk greater than 80. OpenText Identity Governance provides a default list of attributes for selection when creating review definitions. Review Administrators can request Customer, Global or Data Administrators to add other attributes as selection criteria. Items that do not meet the specified criteria in a review definition are filtered out of the review.
Review definitions also assign reviewers based on their relationship to the review items. Often, administrators use review definitions to split up responsibility for reviewing items to prevent bottlenecks and overloading reviewers. Review definitions can also be referenced in certification policies to enable a comprehensive view of your organization's compliance with specific certification controls such as Sarbanes-Oxley Act (SOX) or Health Insurance Portability and Accountability Act (HIPAA).
HINT:For information about certification policies, see Section 27.0, Creating and managing certification policies. Once a review definition is referenced in an active certification policy, it cannot be deleted. For detailed procedures about creating review definitions, see Section 23.1, Creating a review definition
22.1.3 Understanding default selection criteria
|
For Review Object: |
For Review type: |
Specify review items by: |
|---|---|---|
|
Permissions assigned to accounts |
Account Access Review |
NOTE:Specifying identities or applications first helps to determine if users mapped to accounts or custodians of accounts will be reviewed. For more information, see Section 22.1.5, Expanding and restricting review items. |
|
Account Review |
NOTE:Specifying identities or applications first helps to determine if users mapped to accounts or custodians of accounts will be reviewed. For more information, see Section 22.1.5, Expanding and restricting review items. |
|
Business role definitions |
Business Role Definition Review |
|
|
User direct reports |
Direct Reports Review |
Users |
|
Business roles assigned to users |
Business Role Membership Review |
Business roles |
|
Business role authorization |
Business Role Authorization Review |
Business roles |
|
Technical role definitions |
Technical Role Definition Review |
|
|
Global authorizations |
Global Authorization Assignment Review |
Global authorizations NOTE:It is always important to carefully consider the implications when removing any authorization and ensure that the action aligns with your policies. |
|
User Access Review |
NOTE:Optionally, you can further expand or restrict your review items to include items that have been authorized by a business role. For more information, see Section 22.1.5, Expanding and restricting review items. |
|
User profiles |
User Profile Review |
|
22.1.4 Adding selection criteria for review items
In addition to the default selection criteria, you can enable other attributes including custom attributes as selection criteria. In the attribute definition editor of the catalog, an administrator with Data, Customer, or Global Administrator authorization can specify whether an attribute can be used as a review criteria by selecting an attribute in the Data Administration > Attributes pages and specifying Display in review item selection criteria. For example, in the Identity Attributes page, a Data Administrator can enable Job Code as selection criteria and then a Review Administrator can create a review of users based on Job Code value. In the Permission Assignments page, a Data Administrator can enable Assignment Type and then a Review Administrator can create a review of permissions based on assignment type.
HINT:When you specify a boolean attribute in your review criteria and there are null attribute/column values in the database these records will be ignored. Customer, Global, or Data Administrators will need to ensure that there are no null values if you intend to use the attribute as review criteria or add transformation code to convert a null to be true or false or use bulk data update settings to change the null values to true or false. For more information see, Editing attribute values in bulk.
22.1.5 Expanding and restricting review items
In addition to preselected options for specifying review items and additional options based on your review type, you can modify the preselected options and expand or restrict items being reviewed in a User Access Review, an Account Review, or an Account Access Review. The following table provides a few examples of available options and special conditions, if any.
|
If you want to... |
Select |
|---|---|
|
Restrict review items to users as account custodians or mapped accounts |
Users first, then select type of accounts, and specify if the selected users are mapped users or account custodians. NOTE:The ability to indicate if the selected users are mapped users or account custodians will be available only if you select users first and then accounts. |
|
Restrict review items to items that were not authorized by a business role or to items that were authorized by a business role |
Review only items that have not been authorized by a business role or Review only items that have been authorized by a business role. NOTE:If your review items include singular or shared accounts that are either authorized or not authorized by a business role, you can view the authorization details for each review item. This includes information about users, permissions, and whether users are authorized or not for specific permissions. Additionally, if there are any changes to the authorization within the business role during the review process, you can view those updates in the authorization details. |
NOTE:For an account to be authorized by a business role, the application to which the account belongs should be added as an authorized resource for the business role. Estimate impact calculations display an approximate number of review targets and do not include additional options such as business role authorizations in the review target calculations. Start the review in preview mode to get an accurate preview of review items based on all review item selection criteria.
22.1.6 Specifying self-review policy
While creating review definition, administrators can specify self-review policy based on the following review types:
-
User Access Review
-
User Profile Review
-
Account Review
-
Business Role Membership Review
When specifying the self-review policy, you can choose to:
-
Allow self review in all stages regardless of the specified reviewers
-
Send all items that will result in a self review to the exception queue
-
Prevent self review, but allow other reviewers to complete review actions when a review item is assigned to multiple reviewers in a specific review stage
22.1.7 Specifying reviewers
When defining a review, you assign users and roles to perform the review. Depending on the type of review, you can specify any or more than one of the following options as reviewers.
|
For Review type |
Reviewers |
|---|---|
|
User Access |
*Role reviews are two variations of the User Access Review: Technical Role Assigned to Users and Technical Role Detected on Users. |
|
User Profile |
|
|
Accounts |
|
|
Accounts Access |
|
|
Business Role Membership |
|
|
Business Role Definition |
|
|
Technical Role Definition |
|
|
Business Role Authorization |
|
|
Global Authorization Assignment |
|
|
Direct Reports |
|
For more information about owners of applications and permissions, see Section 12.2, Understanding identity, application, and permission management. For more information about coverage maps, see Using coverage maps.
For additional verification or approvals, you might specify more than one reviewer stage. If you specify more than one stage for reviews, the reviewer assignment workflow will vary based on the specified stages. For more information about multistage reviews, see Section 22.1.17, Understanding multistage reviews.
To ensure a timely review process, you can also specify an Escalation Reviewer. Escalation Reviewer resolves all review tasks that are not completed on time. You can specify users, groups, and business roles as Escalation Reviewers. If you do not specify an Escalation Reviewer, the Review Owner is the default Escalation Reviewer. Escalated review items also appear in the Exceptions stage. If the application detects any escalations at the start of a review, all the review items appear in the Exceptions stage.
For more information about authorizations including Escalation Reviewer, see Section 2.1.2, Runtime authorizations.
22.1.8 Setting review expiration policy
Review definitions contain an expiration policy. Review Administrators and owners specify the actions that needs to be taken when a review expires without being completed:
-
Complete the review with any final decisions that have been made and send these to fulfillment and the auditor, if these are defined, and leave all other items with no decision
-
Complete the review with any final decisions that have been made and send these to fulfillment and the auditor, if these are defined, and keep all other items with no user profile changes or with assigned accounts, permissions, roles, or direct report relationship
-
Complete the review with any final decisions that have been made, assign remove or remove assignment decision to all other items, and send all to fulfillment and the auditor, if these are defined
NOTE:This option is not available for User Profile Review, Business Role Definition, and Technical Role Definition Review.
-
Extend the review for a grace period that will continue to renew each time the review expires without being completed or terminated
-
Terminate the review and discard all decisions
For OpenText Identity Governance 2.0 and later, review definitions have the default expiration policy set to complete the review. For review definitions migrated from earlier versions of OpenText Identity Governance, review definitions have the default expiration policy set to terminate the review and discard any decisions.
22.1.9 Setting review notifications
Email notifications let reviewers, escalation reviewers, owners, and others know when a review is at various stages of a review run. The Notifications area of a review definition allows you to set up several standard notifications to go to whomever you specify during the various phases of a review. Standard notifications include Review start, Review end, Reviewer task past due, and Review completion. Review the details of the email notification and update it as needed.
You can click an email name to view who will receive the email, why they will receive it, when they will receive it, and how often they will receive it. You can either accept the default settings or change the settings and add other recipients based on relationships. You can view the name of the email source, preview the email, and email the notification to a specified email address. If you change the default settings, we recommend that you also change the description of the notification. For example, if you change who receives the notification, change the recipient name in the description.
Regarding notifications received by escalation reviewers, when a review item is escalated, a reminder notification is sent to the escalation reviewer as it would to any other next reviewer. By default, the escalation reviewer will not receive the Reviewer task past due notifications as these are typically emailed to the reviewer and reviewer’s supervisor when overdue tasks remain in the reviewer queue. However, you can add an escalation reviewer as a recipient in the CC field if needed.
In addition to changing the settings when defining a review, you can also remove a default notification, customize the template of a default notification, and add new notifications by selecting an email template. For information about customizing the templates, see Section 4.4, Customizing email notification templates. For information about disabling email notifications such as notification when a running review is terminated or notification when permissions are revoked, see Disabling review email notifications.
22.1.10 Scheduling a review
OpenText Identity Governance calculates a schedule based on a specified start time, time interval, the time of the day, and the time zone. You can specify the time interval to be hourly, daily, weekly, monthly, or yearly. For all schedules, the time end date is adjusted automatically based on the Java add calendar method. For weekly and monthly schedules, the next review is determined based on the specified day of the week or day of the month. The following table provides a few examples of weekly and monthly schedules.
|
Start time |
Run every |
Run on |
Time of day |
Next scheduled start time |
|---|---|---|---|---|
|
Tue Sept 14 02:00:00 PM IST 2021 |
1 month |
First Tuesday of every month |
02:00:00 PM |
Tue Oct 05 02:00:00 PM IST 2021 |
|
Mon Sept 20 09:30:00 AM EST 2021 |
1 month |
The last day of every month |
10:00:00 AM |
Sun Oct 31 10:00:00 AM EST 2021 |
|
Wed Sept 15 05:30:00 PM IST 2021 |
3 weeks |
Friday |
06:00:00 PM |
Fri Oct 08 06:00:00 PM IST 2021 |
NOTE:
-
The OpenText Identity Governance server needs a 30-minute gap between runs of the same review. For example, if you schedule a review to run at frequent intervals, allow at least 30 minutes to lapse between the runs. Otherwise, the subsequent runs might fail to start and OpenText Identity Governance does not notify you of the failure. You can control the gap by using the global property com.netiq.iac.scheduling.minTimeBetweenRuns. Contact your SaaS Operations Administrator to enable the global property that controls the gap.
-
For schedules where you select the option after review ends, the review period is considered and the next review cycle is considered based on the end date of the review period. For example, if you schedule a weekly review to run on September 20th 2021, and thereafter run every two weeks, then the next review will be scheduled for October 18th 2021, considering a review period of two weeks.
22.1.11 Previewing a review
Administrators can start a review run, or review instance, in preview mode or live mode. In preview mode, administrators can:
-
Preview review definition version, assigned reviewers, review items, and notification emails
-
View the name of the person who started the review on demand, on schedule, or by micro certification
-
Change review properties such as review owner, auditor, review options, or duration properties
-
If needed, change reviewers per review item or in bulk
-
Preview recipients of notifications
-
Export review items to CSV
-
Track details of review assignment changes
-
Go live
NOTE:Review description and reviewer changes made in preview mode will apply only to the current review instance. Changes made to the Reviews > Definitions, will apply to future review run instances.
22.1.12 Modifying a review definition
Administrators can modify the attributes of a review definition at any time, including the Review Owner. If there is a running review instance at the time, that running review instance is not affected by changes to the definition. A new version of the definition with the changes is created, and only future runs started after the modified definition will reflect the change.
If you have a review currently running, modifying the review definition does not change the attributes of the current review. The running review always points to the version of the review definition that you used to start the review.
If you assign a new owner to a running review instance, both the previous and new owners can access that specific instance of the review. The previous owner continues to see review runs from before the ownership change and future review runs. The new owner sees only that review run. You can also change the review end date and time for a running review.
22.1.13 Reviewing items
When a review run or review instance is live, the server generates review items based on the criteria. Assigned reviewers look at the review item details, decide what action to take on each review item and submit their decisions. If allowed, by the review definition, reviewers might reassign items to a different reviewer instead of making a decision.
In a review with multiple reviewers for each review item, when the first reviewer submits actions for any of the review items, decisions can be seen. When any reviewer has submitted a decision for a review item, the other reviewers cannot take any action on that item unless the reviewer has authorization as an administrator. Review items with no actions remain in each reviewer’s list until someone submits actions for them.
In a review with multiple stages, reviewers must act on review items in the order that the stages are defined in the review definition. For more information about multistage reviews, see Section 22.1.17, Understanding multistage reviews.
NOTE:When OpenText Identity Governance cannot determine an identity associated with an account or functional assignment, such as supervisor, to assign a review item to a specific person, the review owner becomes the assignee for the review item. All review items assigned in this way show in an exceptions section in the list of reviewers on the review owner view.
While reviewing items the reviewers have the option to see the assignment details such as, if the assignment was direct or inherited, assignment start and end time, assignment value and risk. If the permission collector is an AD or an OpenText eDirectory collector, then during collection, they must enable the option Populate Nested Permission Assignments to collect these details.
Time-based assignment information such as removal or expiration of permissions, technical roles, or business role with assignment can also be viewed while reviewing items. Reviewers and review owners of user and account access review, account reviews with account permissions, and business role membership reviews can review the assignment details and decide to keep or remove the assignments before the scheduled time. If they remove any assignment, and the review item is approved, OpenText Identity Governance removes the time-based assignment from the pending requests list. Review items with a clock icon next to it indicates that it has time-based assignment information.
22.1.14 Downloading reviewers and review item lists
You can download all or a filtered list of review items assigned to you as reviewers. In addition, Review Administrators and owners can download list of all reviewers, a list of review items in a specific reviewer’s queue, and a list of all review items. You can download these lists as a CSV file for manual review and comparison.
The list of reviewers includes rows for each reviewer by queue type. For example, if a reviewer is a supervisor and also an exception reviewer, you will see two rows for the user in the downloaded file. When review items are assigned to multiple reviewers, for example when a reviewer is a group, you will see a row for each reviewer with the same number of review items. In all the scenarios, each row will include columns of all the user attributes that were enabled to display in the quick info view in the Data Administration > User menu including custom attributes.
The list of review items you download from the Review Items tab will always include all review items. Except for User Profile Review, all other review item lists will include final decisions made on the review items. User Profile Review will include only the original values of the selected attributes.
The list of review items you download from the Your Review Items tab includes rows for review items assigned to the reviewer with columns that you, as an administrator, included in the Configuration > Review Display Customization menu. You can filter the review items and download only the items you want to review manually.
NOTE:The download list items count will not match the actual number of review items in an Account Review that includes permissions. The count only reflects the number of accounts that match the search criteria. However, all the permissions under each account will also be included in the download resulting in more review items than the number displayed on the review page.
All downloaded files will be saved to a download folder. You can then click the Download icon on the application title bar to access the saved file and download the file to your local machine.
22.1.15 Understanding reviewers and escalation
When you initiate a review run, tasks are generated for the assigned Reviewers. The Reviewers are responsible for reviewing a set of users and deciding whether the current user access should be maintained or revoked, or, in some cases, modified. OpenText Identity Governance can send reminders to the Reviewer or escalate the review items to the Escalation Reviewer, if one was specified in the Review Definition, or to the Review Owner who is the default Escalation Reviewer. Also, review items in the exception queue (unmapped accounts) are automatically assigned to the Escalation Reviewer if an escalation reviewer was specified for that review. In a multistage review, the tasks are forwarded to the next reviewer before it finally moves the tasks to the Escalation Reviewer or Review Owner queue.
Reviews that contain reviewers specified by a coverage map can result in an escalation if no matches could be found from the coverage map. For more information about reviewers, see Section 22.1.7, Specifying reviewers. For more information about managing Reviewers, see Section 25.2.4, Managing the progress of reviewers. For more information about performing a review, see Section 26.1, Performing a review.
22.1.16 Escalating review items
To ensure that the review process proceeds in a timely manner, there are escalation options available to help Review Owners and Administrators. You can set one or more escalation reviewers, and a timeout value to escalate the process and move pending review items to escalation reviewer queues. If a review definition does not set escalation reviewers, the review owner is the default escalation reviewer and in a multistage review, review items will be escalated to the next reviewer in the queue.
NOTE:If a review definition specifies a group as the reviewers and a member of the group is the person being reviewed, the self-review policy is used to determine which group members can review the item. The self-review policy can either allow users to review their own items (self review), send self-review items to the exception queue, or prevent self review but allow other reviewers to complete the item if it is assigned to multiple reviewers in the same stage. For more information about the self-review policy see Section 22.1.6, Specifying self-review policy.
22.1.17 Understanding multistage reviews
If you specify more than one reviewer stage, the reviewers must complete the review in the assigned order. For example, you might want the permission holders to verify that they continue to need the assigned permission, then the individual’s supervisor can approve that ongoing need. As a final step, the permission owners can review the assigned permission. In this case, you would specify Self review, Supervisor, then Permission owners as the reviewers. Each stage shows as a separate group of review items to the review owner. When you select Self Review, users can review their access for that stage only, unless the Review Options are set to Allow self review in all stages.
If you specify more than one reviewer (such as a set of users or groups), each reviewer shares the responsibility for submitting a decision within a single reviewer stage. For example, you might want the permission holders to verify that they continue to need the assigned permission, then you want a group of users called Super group to approve the ongoing need. In this case, you would specify Self review then Review by Selected Users: Super group as the reviewers.
You can also specify that a stage is skipped if the prior stage decision is Keep or Remove. By default, you cannot specify the same reviewer in consequent stages.
At any point during a review run, OpenText Identity Governance might not be able to resolve a reviewer. For example, if you specify Permission owners as one of the reviewers and no permission owner is actually specified in the catalog, it cannot resolve the reviewer to an identity. When this happens, the review item is escalated to the Escalation Reviewer, if one exists, or to the Review Owner, and this reviewer must complete the remaining review tasks for the item. In this situation, the review owner sees an exception section with the review items with the unresolved review items.
Secondary reviewers in a multi-stage review can confirm the previous decision or they can override the decision. For Technical Role and Business Role Definition review they can make additional changes to the review definition or undo or discard the changes.
22.1.18 Completing or terminating a review
Aside from letting the expiration policy complete the review run, a review run concludes in one of several ways:
-
All specified reviewers submit actions for their review items, and the Review Owner approves or terminates the review run.
-
Reviewers do not submit actions for all their review items, and the Review Owner completes the review run.
-
Reviewers do not submit actions for all their review items, and the Review Owner terminates the review run.
After reviewers have made decisions and submitted all review items, the Review Owner approves or terminates the review run and the review run details moves to a list of completed reviews.
A Review Owner has the option to complete an in-progress review even if reviewers have not submitted decisions for all review items. When a Review Owner completes a review, the following actions are taken:
-
Forwards any final decisions that reviewers have made to fulfillment. In multistage reviews, a decision is considered final only when all multi-stage reviewers of a review item have submitted their decisions.
-
Marks the remaining review items Keep, Remove, Keep Assignment, Remove Assignment, No profile changes or as no decision made based on the review definition expiration policy.
-
Shows the review status as a percentage of completion in review history.
A Review Owner also has the option to terminate an in-progress review. When a Review Owner terminates a review, the following actions are taken:
-
Does not forward anything to fulfillment
-
Marks the review run as terminated
22.1.19 Understanding the fulfillment process for review changes
The source of the identities, permissions, accounts, and roles under review drives how review-related request changes are fulfilled. The fulfillment process can be manual tasks, automated actions in OpenText Identity Manager, actions sent to help desk services, or actions initiated by workflows in OpenText Identity Manager. The fulfillment process begins when a review run completes or when a Review Owner or Administrator modifies or removes a review item, it generates a change request which are then sent to fulfillment for approval. Each review item generates separate change request. However, for Business Role Authorization Review, the review items are consolidated into a single change request, which is then forwarded to fulfillment.
Note that, for Global Authorization Assignment review types, OpenText Identity Governance fulfills the change requests through its internal process and does not initiate a separate request.
Review items for entities, such as a role, permission, account, or user if they are deleted before approval, it does not generate change requests. In such cases, the deleted entities are marked with a strike-through line across the text and also provides the reason for not generating the fulfillment request under View Fulfillment Status.
For Technical Role Definitions review, when you generate a fulfillment request due to attribute change or permission revocation, the requests are automatically fulfilled on approval. But there are scenarios when the requests are sent for manual fulfillment. Following are those scenarios:
-
When the value of a single-valued attribute, for example, risk has changed since the review started
-
When a category marked for removal is no longer associated with the role
-
When a permission marked for revocation is no longer assigned to the role
-
When internal fulfillment is not enabled
-
When special fulfillment instructions are specified
Sometimes multiple changes per review items are split between automatic and manual fulfillment. In such scenarios, some changes are fulfilled automatically and the remaining are sent for manual fulfillment.
You can, however, send all requests generating from Technical Role Definition review for manual fulfillment if the global property com.netiq.iac.fulfillment.techrole.manualonly is set. Contact your SaaS Operations Administrator to set the property.
There are scenarios when request items get forwarded for manual fulfillment. For example, when the fulfillment target is Active Directory, and there is a request to remove an inherited permission from a user. When a user is assigned a permission to a group because they are a member of that group, it is a direct assignment. However, there are times, when a user is assigned permission to a group even when they are not a direct member. This happens when the groups are embedded. In such scenarios, the user inherits the permission and OpenText Identity Governance fails to automatically fulfill the request since the user is not part of the group. To collect these permission assignments, you must enable the option Populate Nested Permission Assignments while configuring the OpenText Identity Governance AD Permission and eDir Permission collector templates.
Review Owners and Administrators can view the fulfillment status of review items automatically fulfilled and verified by internal processes as soon as a review run is partially or fully approved.
For more information about fulfillment, see Section 14.1, Understanding the fulfillment process.
22.1.20 Managing the audit process
Some review definitions require a Review Auditor to certify the results of the review run. Review Auditors are individuals who have read-only access to a review run. They cannot modify or delete decisions. They can:
-
View the review definition used for the review run
-
View reviewers and decision statistics
-
View review items and related activity
-
Download list of reviewers and their respective queue statistics as a CSV file
-
Download list of all review items as a CSV file
-
Accept the review
-
Enter comments for rejection and reject the review
NOTE:All decisions and run history are retained even if the review is rejected.
When a review run is waiting for acceptance an email notification is sent to the Review Auditor. The Review Auditor can then log in and can review all details and Accept or Reject the review. The Review Auditor must enter comments when rejecting a review.
22.1.21 Creating certification policies and remediating violations
A Customer, Global, Review, or Data Administrator creates certification policies and sets remediation action for violations. The violations are calculated and after initial setup automatically triggers remediation action. Remediation actions include email notifications, change requests, or micro certification.
For more information about micro certification and certification policies, see Section 22.2, Understanding micro certification and Section 27.0, Creating and managing certification policies.